

Tesla’s Financial Slide Deepens After Musk’s White House Exit
Prime Highlights Tesla Q2 2025 sales fall 12% as car sales implode. Elon Musk scandals pile layers of complexity on top of brand collapse and internal turmoil. Key Facts Regulatory credit sales fell by more than 50%, damaging Tesla’s margins significantly. Operating margin fell to a low of 4.1%, after the weak fundamentals. Key Background Tesla Q2 2025 quarterly report sees the financial crisis worsening, as the EV giant struggled with dwindling revenues and profits. Overall revenue dropped 12% from year ago to $22.4 billion, with automobile sales decreasing by 16%. Tesla’s net profit declined 16% to $1.2 billion, consistent with weakened demand and mounting pressure from international EV competitors. The most worrying was a drop of 21% in California sales, the largest U.S. market for Tesla. The firm’s earlier dependable carbon credit and regulatory revenues took a huge hit, to paltry $490 million—below half-time levels. That hurt Tesla’s bottom line right away, taking operating margins down to just 4.1%. Once feted for double-digit margins, Tesla is now confronted with mounting operating and financial stress as its primary profit streams dwindle. At the center of Tesla’s troubles is the growing reputational price tag of Elon Musk’s politicking. His short-lived dalliance with the Trump administration’s “Department of Government Efficiency” triggered a public outcry on a massive scale. The move triggered mass protests, burning of Tesla showrooms, and worldwide demands for a boycott of the firm. This backlash further alienated one of its largest customer bases and solidified Tesla’s public image. To the company’s behind-the-scenes distress is added an exodus of high-level executives, including North American sales head. Sources point to internal discontent with Musk’s politics and continuing worsening performance as reasons for leadership shake-up. Behind the scenes, competitors such as BYD continue to nibble at Tesla’s global market share. Forward-looking, Tesla hopes its future robotaxi fleet and Supercharger expansion will spur non-vehicle revenues. Both entities, though, face regulatory as well as intense competition hurdles. With U.S. EV incentives also set to expire for Tesla buyers, the prognosis seems increasingly grim. Read More: Trump Secures Historic $550 Billion US–Japan Trade Deal with 15% Tariff Accord
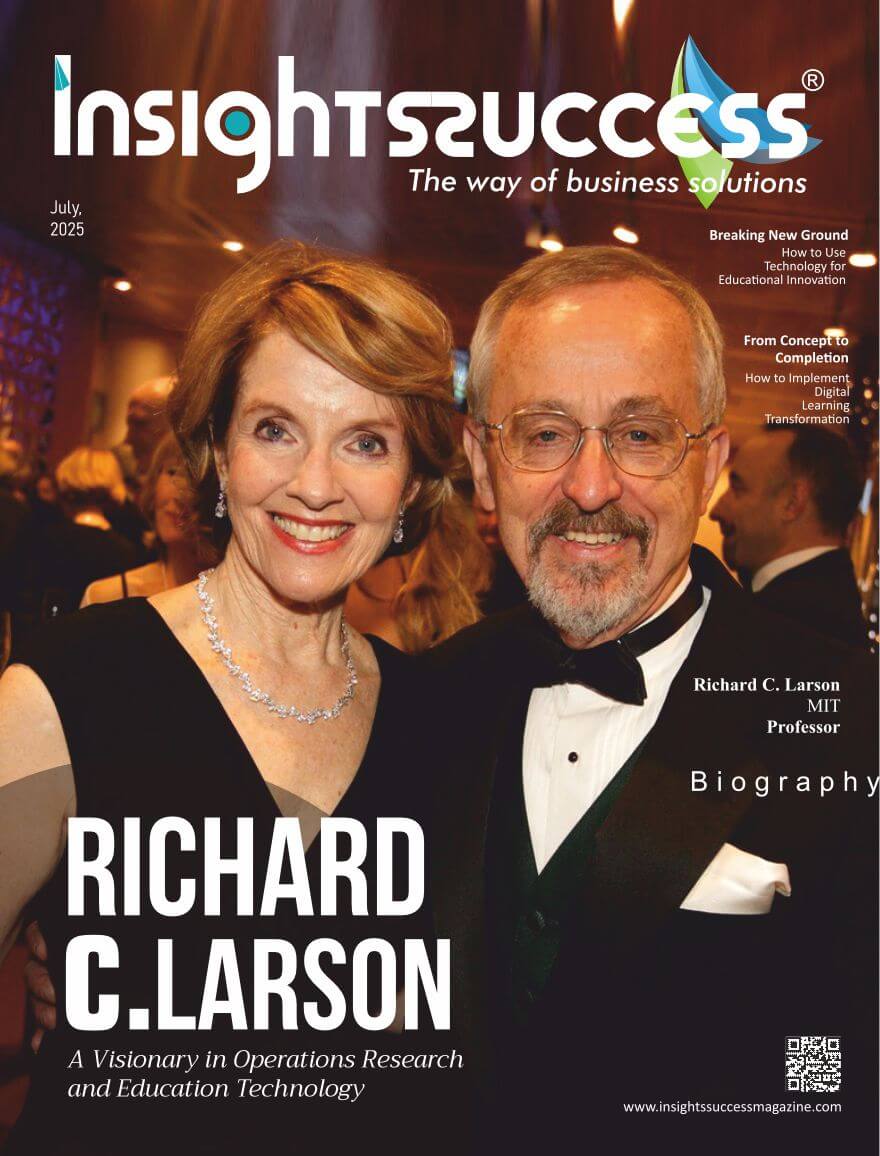
The Architect of Learning The Richard Larson Legacy
The Architect of Learning The Richard Larson Legacy This edition honors Richard Larson’s transformative contributions to education, exploring his groundbreaking work in learning systems, technology-driven instruction, and academic innovation. It captures his lifelong mission to redefine how knowledge is delivered, empowering future generations through visionary thinking and a passion for accessible, impactful learning.

Most Pioneering Leader Rewriting the Blueprint for Queueing & Urban
Most Pioneering Leader Rewriting the Blueprint for Queueing & Urban In the intersecting worlds of mathematics, urban planning, and human behavior, few figures have left a more enduring impact than Richard C. Larson, affectionately known as “Dr. Queue.” With decades of groundbreaking research at MIT, Richard has become one of the most pioneering global leaders in applying quantitative analysis to real-world urban and infrastructural challenges. Quick highlights

Model-Based Thinking: Richard Larson’s Lifelong Mission to Improve Everyday Life Through Analytics
Dr. Richard Larson’s name is etched in the world of operations research not just as a theorist, but as a problem-solver whose career has spanned more than five decades. His influence stretches across city infrastructure, emergency response, education, and public policy. As a professor at the Massachusetts Institute of Technology (MIT) since 1969, and now Professor Emeritus, Dr. Richard has devoted his life to applying mathematical models in ways that tangibly improve lives. From the optimization of police dispatch systems to the transformation of educational methodologies, his body of work illustrates a rare fusion of academic rigor and practical relevance. Driven by the belief that mathematics can be a tool of empowerment rather than abstraction, Dr. Larson has sought to close the gap between theoretical constructs and their real-world applications. His career serves as a testament to how deeply one person can impact the world when committed to analytical thinking and human-centered innovation. In the classroom, through public service, and within private enterprises, his approach—model-based thinking—has revolutionized the way decisions are made at both individual and systemic levels. This exploration of Dr. Richard’s legacy sheds light not only on his intellectual contributions but also on his enduring dedication to mentoring, teaching, and influencing the next generation of thinkers. He proves that even the most complex mathematical frameworks can serve deeply humane purposes: reducing suffering, expanding access to knowledge, and improving the quality of life for countless people. As he continues to champion these causes post-retirement, his impact only broadens. Lifelong Commitment to Practical Analytics Dr. Richard Larson has long emphasized the importance of mathematics and analytics in addressing real-world problems. Rather than view operations research as confined to classrooms or laboratories, he treats it as a living toolset with vast potential for social impact. From the earliest days of his career, he positioned himself as a translator between the abstract language of math and the tangible needs of communities. The mentorship of Professor Al Drake played a pivotal role in shaping this philosophy. It was Drake who invited a young Dr. Richard to attend MIT—an invitation that would define the trajectory of his life. What began as a student-teacher relationship blossomed into a lifelong intellectual journey, culminating in a 54-year tenure at one of the world’s most prestigious institutions. At MIT, Dr. Richard Larson didn’t just teach theories—he deployed them. Whether he was optimizing ambulance routes or redesigning educational delivery methods, he made sure his work remained anchored in everyday experiences. His approach has consistently emphasized measurable outcomes. By prioritizing public benefit over academic acclaim, Dr. Richard Larson established a reputation not just as a brilliant mind, but as a problem-solver who never lost sight of humanity. Building Models That Save Lives Among Dr. Richard’s most groundbreaking contributions is the Hypercube Queuing Model, a framework that fundamentally reshaped how emergency services operate in urban environments. Co-founding firms such as ENFORTH Corporation and Q.E.D., Dr. Richard extended his influence well beyond academic circles. These ventures sought to democratize access to advanced research, ensuring that ideas developed in institutions like MIT found applications on the streets and in government offices. The Hypercube Queuing Model exemplifies the potency of model-based thinking. By analyzing and predicting call volumes, response times, and resource availability, the model allowed cities to optimize the deployment of police cars, fire engines, and ambulances. The outcome? Faster response times, better resource allocation, and ultimately, lives saved. This project illustrated Dr. Richard’s belief in “useful mathematics”—not math for math’s sake, but for societal betterment. He understood that behind every data point was a person in need, and every improved second in response time could mean the difference between life and death. Making Knowledge Accessible for All Education is another arena where Dr. Richard Larson has left an indelible mark. Recognizing the barriers that prevent many students from accessing high-quality STEM education, he co-founded MIT BLOSSOMS—Blended Learning Open-Source Science or Math Studies. This initiative democratizes learning by offering free video lessons in math and science to students around the world. Working alongside MIT professor Dan Frey and his late wife, Mary Elizabeth Murray, Dr. Richard Larson envisioned a platform where learning could transcend borders, budgets, and bandwidth limitations. By leveraging the power of digital platforms like YouTube, MIT BLOSSOMS became one of the earliest large-scale open-source educational repositories. The initiative reflects Dr. Richard’s broader philosophy: that knowledge should be a public good. Whether through textbooks, lectures, or open-access resources, he has consistently pushed for education that is inclusive, engaging, and globally impactful. Thought Leadership in Operations Research Dr. Richard Larson has not only advanced operations research through practice but also through leadership. He served as the president of both the Operations Research Society of America (ORSA) and the Institute for Operations Research and Management Sciences (INFORMS)—two of the field’s most respected institutions. Under his leadership, these organizations emphasized interdisciplinary collaboration and knowledge dissemination. He championed the idea that the most effective solutions often arise at the intersection of fields—where math meets public policy, or where engineering meets sociology. His influence also extended to nurturing future leaders in the field. Through conferences, journal contributions, and mentorship, Dr. Richard cultivated a culture of openness, curiosity, and real-world impact that continues to inspire. Model-Based Thinking for Daily Decisions In 2023, Dr. Richard Larson released his most recent work, “Model Thinking for Everyday Life,” published by INFORMS. This book distills his lifelong passion for structured reasoning into a guide for laypeople. It offers readers accessible tools to approach everyday dilemmas—from choosing the fastest route home to making financial decisions—with the same clarity and logic used in professional operations research. This endeavor marks an evolution in his mission: bringing model-based thinking out of the lab and into living rooms. With characteristic humility and clarity, Dr. Richard Larson explains how everyone—not just mathematicians—can benefit from analytical models. He hopes the book helps readers realize that good decision-making isn’t just instinctual—it can be taught, practiced, and refined. In doing so, he demystifies analytics and brings its power into

The Most Trusted Cybersecurity Companies to Watch in 2025
The Most Trusted Cybersecurity Companies to Watch in 2025 This edition highlights the most trusted cybersecurity companies set to shape 2025, showcasing pioneers delivering innovative, reliable solutions to counter growing digital threats and ensure robust protection for organizations across industries. Quick highlights Quick reads

Trust at the Core – Intertec Systems: Building Cyber Resilience for a Secure Digital Tomorrow
Trust is the cornerstone of cybersecurity in the digital era that is evolving at a breakneck speed. That’s why, soon after its establishment in 1991 as an IT infrastructure provider, Intertec Systems transformed into a comprehensive digital transformation partner, expanding its capabilities across applications, managed services, cybersecurity, and cloud solutions. Its evolution has always been driven by a deep commitment to listening to its customers and continuously reinventing itself to meet not only its current needs but also future challenges. Pioneering Innovation: From Managed Services to Smart, Sector-Specific Solutions Intertec Systems was among the pioneers of managed services in the region and executed one of the first cloud migrations to Azure North DC. Today, it continues to innovate with a portfolio of industry-focused intellectual properties, including inspection solutions for municipalities, tailored platforms for the insurance sector, enterprise portfolio management systems, and advanced asset tracking and lifecycle management solutions—integrated with drones and visual asset intelligence. These innovations reflect the company’s dedication to delivering practical, forward-thinking solutions that create real value. From Infra to Intelligence: The Cybersecurity Transformation Intertec Systems has come a long way since its early focus on security product deployments and being a part of Infra Solutions. Over time, it evolved into a trusted provider of cybersecurity consulting and technical advisory services. As one of the early system integrators to establish a dedicated cybersecurity business unit, it has consistently stayed ahead of the curve. Today, its capabilities span Managed Security Services, GRC solutions and consulting, Security Testing Services, and a strong emphasis on Data and Identity Security—an area experiencing significant growth and momentum. Unified Defense: IT, IoT, and OT Secured Together Intertec Systems’s cybersecurity framework also integrates IoT and OT security, forming a unified fabric that supports comprehensive threat defense. The Cybersecurity Resilience Center (CSRC) is now fully equipped to manage OT Security Operations (SecOps), enabling seamless coordination across OT, IoT, and IT environments. This integration is critical for delivering rapid, precise responses to an increasingly complex threat landscape. A Future-Proof Vision: AI at the Heart of Cybersecurity Looking ahead, the future of cybersecurity lies in proactive monitoring, swift incident response, and advanced threat intelligence. Intertec Systems is embedding AI into enterprise security frameworks to empower organizations to anticipate and neutralize threats—before they surface. A Fortress of Cyber Resilience: Six Pillars of Protection Intertec Systems delivers a robust and integrated cybersecurity portfolio built around six core pillars. At the heart of its operations is the Cybersecurity Resilience Center, offering advanced services such as Managed Detection and Response (MNDR), Next-Gen SOC, Managed Endpoint Services, Vulnerability Scanning, Patch and Asset Management, and Disaster Recovery Planning. It was named a contender in IDC GCC Managed Security Services MarketScape in 2023 and a major player in IDC Middle East Managed Detection and Response MarketScape 2024. Sector-Driven Security: Tailored for Every Industry With over three decades of experience, offices in five countries and customer presence in over fifteen countries, Intertec combines deep industry knowledge with innovative technology to deliver customized, resilient cybersecurity solutions. It has a strong presence across Public Sector, Banking & Finance, Healthcare, Insurance, Energy & Utilities, and Enterprise domains. Intertec Systems’s sector-specific expertise allows it to understand the unique regulatory, operational, and threat landscapes of each industry. For example, in banking and finance, the priority is for advanced threat detection, secure transaction frameworks, and compliance-driven controls. In healthcare, the company focuses on protecting sensitive patient data and securing medical IoT (IMoT) environments. For the public sector, it enables secure citizen services and critical infrastructure protection, while in energy and utilities, it addresses OT/IoT security and IEC 62443 compliance. By aligning cybersecurity strategies with industry-specific needs, Intertec empowers organizations to innovate securely, maintain compliance, and build long-term resilience in an increasingly complex threat landscape. Beyond Defense: Building Resilience That Lasts Intertec Systems goes beyond traditional cybersecurity by helping organizations build true cyber resilience—ensuring business continuity even in the face of sophisticated cyber threats. Its approach integrates advanced threat detection, proactive risk management, and automated response mechanisms across IT, OT, and cloud environments. Through its AI-powered CSRC and Managed Services, Intertec Systems provides continuous monitoring, threat hunting, and incident response. The company supports clients in preparing for and recovering from disruptions through disaster recovery and business continuity planning that is aligned with global standards. Its layered defense strategy incorporates Zero Trust Architecture, Automated Moving Target Defense, and User and Entity Behavior Analytics to detect and contain threats before they escalate. Additionally, it offers cloud-native protection (CNAPP), DevSecOps integration, and Data Security Posture Management to ensure resilience across hybrid and multi-cloud environments. By embedding security into every layer—from infrastructure and applications to identity and data—Intertec empowers organizations to defend against attacks, recover swiftly, maintain operational continuity, and adapt confidently to an evolving threat landscape. AI-First Cybersecurity: Intelligence That Learns and Adapts Intertec Systems is at the forefront of integrating AI and automation into cybersecurity, enabling secure digital transformation and building resilient enterprises. Its AI-first approach enhances visibility into internal and external risks, allowing organizations to conduct comprehensive AI risk assessments, implement mitigation strategies, and continuously monitor their security posture. Through its AI-powered CSRC/ SOC with XDR capabilities, the company delivers adaptive protection, behavioral analytics for zero-day threat detection, and orchestrated automated responses. Intertec CSRC further strengthens this capability with predictive recovery planning, autonomous infrastructure testing, and deep and dark web monitoring. The firm also ensures secure AI adoption by safeguarding sensitive data, preventing exposure to large language models (LLMs), and enforcing continuous security posture management. In addition, it leverages AI for proactive threat hunting, automated breach response, and real-time anomaly detection. With strategic partnerships, certified expertise, and advanced AI capabilities, Intertec Systems is enhancing how organizations detect, respond to, and recover from cyber threats—delivering intelligent, end-to-end cybersecurity solutions in an AI-driven world. Governance That Guards: Streamlined Risk, Compliance & ESG Intertec’s Unified GRC solutions help organizations manage risk, ensure compliance, performance, and address ESG requirements. In the realm of Data Security & Governance, it provides capabilities like Data Security Posture Management, Data Loss

Setting New Benchmarks for Data Protection
Trusted and Tested Data protection is no longer a legal compliance issue in an age characterized by the growing digital footprint and ever-more complex cyber threats, but a strategic pillar. Companies must now gain stakeholder confidence through ensuring data security that is not only “trusted but tried” but also through unprecedented levels of technical innovation, governance, measurement, and regulatory preparedness. Institutionalizing Data Protection: Governance as Bedrock Governance frameworks on data protection are now fundamental. According to a recent scholarly report, there is significant value in rigorous frameworks that bind risk management, access control, data quality assurances, and compliance procedures, such as GDPR, HIPAA, and CCPA. Companies that integrate these structures, such as vendor and breach checks, data mapping, and privacy impact assessments (PIAs), show significantly higher data responsibility and resilience. The Rise of Measurement and KPIs Organizational leaders are no longer interested in implementing privacy programs as check-the-box activities. According to the benchmark research conducted by TrustArc in 2025, organisations that monitor their privacy using KPIs (including the number of breaches, time to triage data subject access requests (DSARs), and the number of privacy impact assessments (PIA)) achieve a 100-point privacy maturity rating, compared to the likes of 55 points when no metrics are shown. Just one in five firms is taking advantage of commercial privacy platforms as much as possible, but those have privacy index scores averaging 78%, as compared to 54% in average use by those using open-source or manual tools. Technology Defenses: Automation, AI, and Zero‑Trust Contemporary data protection requires automation. Compliance platforms powered with AI, as provided by TrustArc or OneTrust, allow real-time risk detection, tracking consent, and automating reporting across rapidly changing regulatory landscapes. At the same time, zero‑trust Architecture (ZTA) with strong identity control and active verification has become a paradigmatic standard, not a best practice alternative. ML-driven threat detection tools, extended detection and response (XDR), and anomaly-detection systems are assisting in accelerating breach detection and response within organizations, including by decreasing the duration of detection. Evolving Technical Standards and Privacy‑Enhancing Technologies (PETs) Technical frameworks protecting and ensuring compliance are enhanced by new standards such as ISO/IEC 27040 (Storage security and backup systems) and NIST SP 800-209. In 2025, Privacy Enhancing Technologies (differential privacy, homomorphic encryption, secure multi‑party computation, etc.) are becoming more piloted and allow for making data processing safer without larger utility losses. Barriers Enterprises are also implementing data clean rooms and decentralized identity frameworks to facilitate privileged, secure data sharing with partners without compromising personal privacy. Resilience as Compliance: DORA, NIS2 and Cyber Resilience Alongside privacy regulation, emerging standards, such as the NIS2 Directive and Digital Operational Resilience Act (DORA) in the EU, are also pushing the envelope on aspects of availability, incident reporting, and supply chain protection. Such regulations require organizations, particularly those in critical services and finance, to prove incident readiness, keep the business-continuity procedures, and make the investment in cyber-resilience measures. Privacy leaders are also supposed to handle not only confidentiality but also integrity and availability. Regulations and Global Harmonization There is a new frontier of data privacy laws being enacted. India offers the Digital Personal Data Protection Act (2023) by example, now requiring the aspect of fiduciary duties, penalties, and fines on gaps, and a new Data Protection Board to adjudicate. Simultaneously, the European GDPR and the Californian CCPA are inspiring more than a dozen states in the United States to create their own regulation, resulting in a Swiss-iness that is leading to the call to harmonize through a new proposed Global Data Privacy Alliance (GDPA). Many organizations are adjusting to these international guidelines, such as ISO 27701, APEC CBPR, Nymity PMAF, and others that make accountability result oriented. Benchmarking Cyber‑Insurance and Risk Transfer There is a growing demand for cyber insurance due to the rising breach expenses and ransomware attacks. In modern premiums, validation of robust security postures matters, with immortal backups, incident-response planning, and XDR deployments all being solid underwriting factors. Firms negotiating coverage have an obligation to demonstrate vetted capabilities, continuous back-ups, immutable vaults, and disaster recovery drills, which indicate reliable data protection. Strategic Outcomes: Trust and Stakeholder Confidence The stakeholders are already leaning towards organizations that have been able to integrate governance, measurement, robust technical controls, resilience planning, and compliance with regulations. TrustArc statistics indicate that close to 47 percent of stakeholders currently trust the data protection of trusted organizations unreservedly- an increase that is stunning compared to last year. Businesses that support strategy with quantifiable outcomes not only fear fines but also stand out as brands encompassing privacy ethics and regulatory excellence. Realizing “Trusted and Tested” Protection The new standard of data protection is a combination of governance maturity, quantitative KPIs, sophisticated controls (AI, ZTA, PETs), and regulatory-aligned resilience activities. To be trusted and tested does not merely imply checking off compliances; it means the incorporation of privacy and resiliency at every organizational stratum, including technical, procedural, legal, and cultural. Those organizations that use governance frameworks as their strategic infrastructure, implement platform-based privacy tools and metrics that can be enforced, and demonstrate incident readiness are the new standard-setters-they are turning privacy into a competitive edge rather than a liability. Read More: Masters of Cybersecurity Automation Tools
Masters of Cybersecurity Automation Tools
Behind the Firewall As cyber threats become more advanced, organizations are considering the use of cybersecurity automation tools to strengthen their defenses. Such systems not only increase the level of security but also make the work of teams work radically differently, significantly reducing manual labor and response time. This article addresses major actors, advantages, risks, and new directions in the automation of cybersecurity. Why Automate? Traditional Security Operations Centers (SOCs) faced the problem of alert fatigue for years: constant manual triaging, false positives, and disparate tools, which did not allow prompt action. Tools aimed at automating cybersecurity, such as Security Information & Event Management (SIEM) and SOAR, ease this load by automating (more), reacting (more), and performing activities (more). Use of automated systems allows SOC analysts to give attention to strategic threats instead of routine notifications. In addition, human defenses are no longer sufficient as attackers are automated using AI. Automation serves as a powerful force multiplier, enabling organizations to counter AI-driven threats with AI-driven defenses. However, it is not a fully autonomous solution, as expert oversight remains essential to guide, validate, and refine automated actions. Leading Solutions Here’s a rapid-fire overview of top cybersecurity automation tools shaping today’s defense landscape: IBM QRadar (SIEM/SOAR) QRadar automatically identifies incidents and prioritizes risks through analytics and automated playbooks, which makes busy days much less stressful. Palo Alto Networks Cortex XSOAR The Cortex XSOAR provides streamlined incident coordination and automation, with fully customizable playbooks, support of hundreds of tools, and integration into the SOAR platform. Splunk Phantom / Enterprise Security Splunk ES offers profound analytics, and Phantom manages case management and orchestration. They both automate workflows, alerting, and threat hunting, but complexity and cost are barriers. Tenable.io and Qualys Cloud Platform They are automated tools that conduct vulnerability checks, continuous checks, and remediation planning, which are the core components of proactive threat prevention. Ansible & Puppet (Configuration Management) They are useful in DevOps, but they also automate security baselines, patching, and compliance, keeping secure configurations within enterprises. Darktrace & AI‑driven XDRs Anomaly detection with the help of self-learning AI and the capability of automatic containment is leveraged by platforms such as Darktrace. These new-age tools are opening the door to the future of defense. Challenges & Cautions Although promising, cybersecurity automation tools are still a long way from being plug-and-play. The process of integrating platforms such as Cortex XSOAR and Splunk is also complicated, demanding extensive planning, configuration skills, and valuable time, which may become an actual challenge to smaller or less-resourced teams. The economic and expertise requirements of leading-edge platforms like Splunk ES and QRadar are also a challenge, which can require specific people to handle and monitor them properly. Another crucial thing is trust. Although there is a growing acceptance of AI-based cybersecurity among executives, the same survey carried out by Techradar found that only one in every ten security analysts has complete trust in automated tools. Closing this divide will necessitate more explainability and transparency of the algorithm behavior of such systems. In addition, attackers are now adopting automation as well and can use it to expand and accelerate their threats. This is an arms race where defensive automation has to keep up in speed. Future Trends Automation and machine learning are used by platforms like ReliaQuest GreyMatter and vulnerability detection models that use AI to provide fast and data-driven incident detection and response. The DevSecOps arena is experiencing a radical shift in the practicality of penetration testing, as effective human control is still a necessity because AI tools such as PenTest++ are automatically creating tests and finding possible exploits. Standardized automation protocols, such as SCAP frameworks and IEC 62443 standards, are becoming more notable in facilitating interoperable, policy-based security automation in industrial control systems and critical infrastructure. In the future, projects such as Google Big Sleep herald the advent of autonomous cyber-AI, or systems capable of identifying, investigating, and blocking threats independently of direct interaction with the human operator, a significant step in terms of cyberspace protection of a preventive nature. Final Thoughts Cybersecurity automation tools are no longer optional improvement addons; they are now key defenses. Although powerful, effective deployment needs a strategy that includes selecting the right tools (SIEM, SOAR, EDR, XDR, vulnerability scanners, configuration enforcers), building analyst trust, and maintaining control. The future holds even more autonomy: self-testing, non-UI AI agents, and standards-driven policies. Nevertheless, the cardinal rule remains that technology can support and enhance cybersecurity efforts, but it cannot replace the critical judgment and expertise of human professionals. Teams with a mastery of automation will be able to stay ahead of the evolving digital threat and respond rapidly, intelligently, and with resilience as we go behind the firewall. Read More: Setting New Benchmarks for Data Protection

Trump Secures Historic $550 Billion US–Japan Trade Deal with 15% Tariff Accord
Prime Highlights President Trump signs a $550 billion trade pact with Japan, putting a flat 15% tariff on Japanese imports. The agreement opens Japanese markets to US agriculture, autos, and energy, enhancing American job prospects. Key Facts Japan agrees to invest $550 billion in the US where 90% of the returns will accrue to the American economy. The agreement avoids higher tariffs previously threatened and excludes steel and aluminum from reductions. Key Background In a stunning economic move, former President Donald Trump has unveiled what he refers to as the “largest trade deal in history” between the United States and Japan. This comprehensive deal levies a flat 15% reciprocal tariff on Japanese exports, significantly lower than the earlier proposed 25% to 27.5%. The tariff is applied to most goods, from Japanese cars and industrial goods, but most importantly, does not apply to steel and aluminum, which will continue to have a 50% tariff. The crown jewel of the deal is Japan’s commitment to a record $550 billion investment in the US economy. The economic stimulus will be provided in the form of structured loans and infrastructure projects, as well as a large liquefied natural gas (LNG) project on Alaska. President Trump emphasized that nearly 90% of the benefits from this investment would remain in the United States, an argument he made as a win for American workers and companies. In return, Japan is committing to open up its market to many of America’s top exports like automobiles, rice, beef, and other farm products. America’s farm and manufacturing industries are most likely to benefit with enhanced access. Trump indicated that the deal will help create hundreds of thousands of American jobs and stabilize supply lines in both nations. The agreement also set off a positive market reaction, with Japan’s stock market Nikkei 225 surging and automakers such as Toyota, Honda, and Nissan posting double-digit stock gains. Economists view the level flat 15% tariff as a step in a more unshackled and reciprocal approach to trade policy than Trump’s earlier segmented tariff approach. Japanese Prime Minister Shigeru Ishiba indicated cautious support, noting the significance of the deal but adding that full legislative review would follow later. The deal is part of Trump’s broader “Liberation Day” trade reform initiative, with similar deals in negotiation with Southeast Asia and negotiations scheduled later this year with China and the EU. Read More: Tesla’s Financial Slide Deepens After Musk’s White House Exit

The Most Successful CSO Redefining Success in 2025
The Most Successful CSO Redefining Success in 2025 Sultan Ahmed Alghfeli, Chief Strategy Officer at Emarat, exemplifies visionary leadership in driving innovation and sustainable transformation. With cross-industry expertise and a people-first philosophy, he redefines Emarat’s role from a fuel provider to a future-focused mobility hub, aligning national priorities with customer-centric, technology-driven growth. Quick highlights Quick reads




