
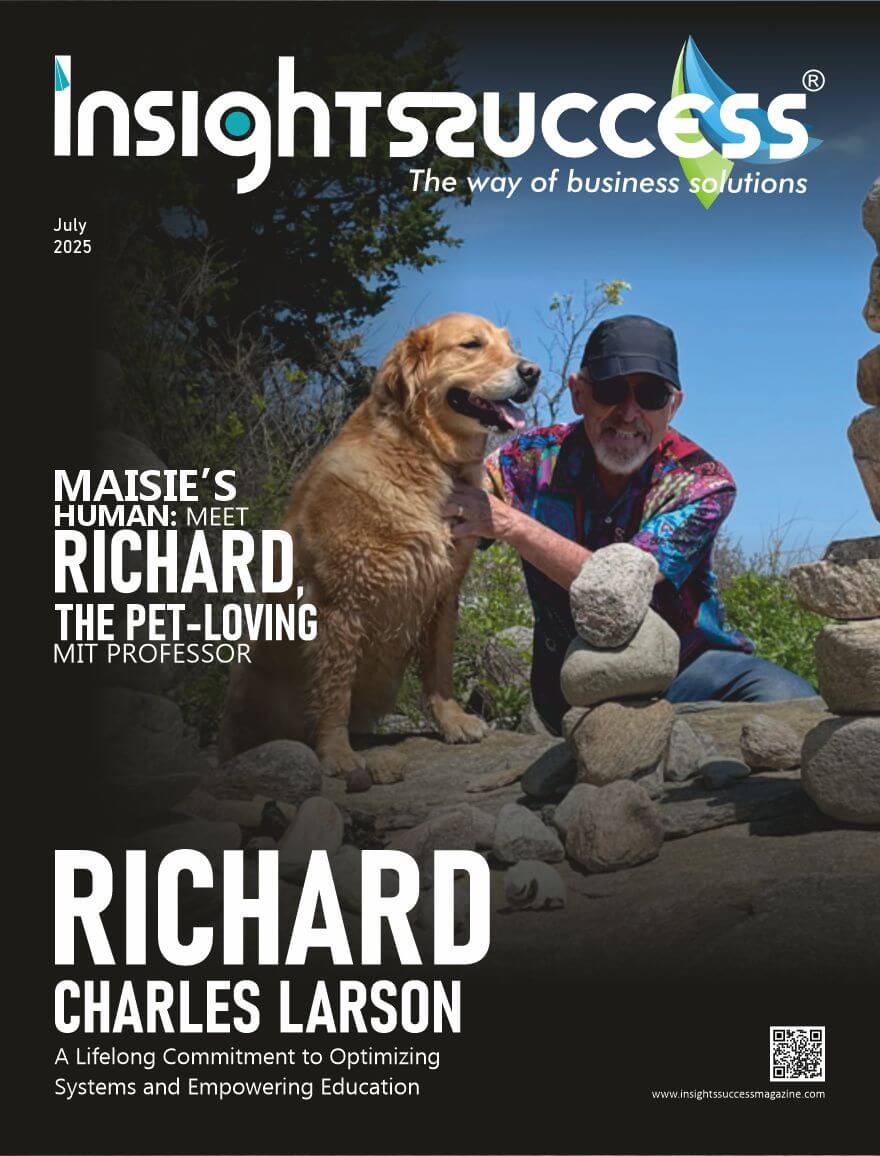
Maisie’s Human: Meet Richard, the Pet-Loving MIT Professor
Maisie’s Human: Meet Richard, the Pet-Loving MIT Professor This edition celebrates Richard Larson, MIT’s “Doctor Queue,” for his transformative leadership in Operations Research. Blending sharp analysis with deep care, he tackles urban chaos and long waits, always prioritizing people. With his golden retriever Maisie, Larson’s humane approach reshapes systems for a more equitable future. Quick highlights Quick reads

Balancing Technology and Traditional Teaching Methods for a Blended Learning
Blended learning, a hybrid model that mixes classical teaching with contemporary technology, is a revolutionary model of education. Merging the benefits of face-to-face teaching with digital applications, it provides a flexible, active, and tailored learning process. But the right balance between technology and traditional teaching is essential to achieve maximum efficiency from it. This article examines the tenets, advantages, difficulties, and the means to balance these practices in order to develop an ideal blended learning environment. Knowing Blended Learning Blended learning is face-to-face training augmented with digital materials so as to create an enthusiastic learning setting. Traditional methods, such as lectures, dialogues, and practical activities, provide order, person-to-person interaction and immediate feedback. Technology, on the other hand offers multimedia content, interactive space, and information-rich understanding and enables self-guided learning and accessibility. Its vision is to take the benefit of both to enhance better performance of students without disregarding the differences among students. Advantages of Blended Learning Blended Learning has a number of advantages. First of all, it is flexible. The students can access the resources online and can do the learning at their own time but still get the face to face instructions without geographical restrictions. As an example, a lecture recorded after a classroom lecture, or a quiz can reinforce classroom lectures, outside of scheduled time. Second, it increases individualization. The online services are likely to include the feature of adaptive learning software that helps them customize it to the particular requirements of a student. To illustrate, programs like the Khan Academy or Google Classroom are able to moderate the complexity of the content based on the student. This will enable each child to be challenged in the way that is appropriate. In comparison, the conventional operation gives teachers the chance to provide comprehensive assistance through individual work or group work. Third, blended learning promotes immersion. Video and simulations, as well as interactive games that are considered multimedia resources, make learning process more attractive and interactive. Combined with the face-to-face work such as debates or practical experiments, they create a comprehensive and dynamic environment, which accommodates a variety of learning styles. Lastly, it readies students for the future. Through technology integration, students gain digital literacy skills needed in today’s workplaces. At the same time, conventional methods develop soft skills such as communication and teamwork to ensure a balanced education. Challenges of Balancing Technology and Traditional Methods While it has benefits, blended learning has issues. Too much technology can lose the human element that classroom instruction generally produces. Without balance, students can become isolated when online portions are predominant, limiting opportunities for student interaction or teacher guidance. In contrast, too much emphasis on the traditional approach can restrict exposure to new tools, making scalability and adaptability difficult. Digital divide is another challenge. Not everyone has consistent access to devices or internet speeds, building inequalities in learning experiences. The schools have to counteract these imbalances to promote inclusivity. Teachers also risk a cliff effect when they implement new technologies, demanding continued training and support. Student interest must also be maintained. Technology can be fascinating, yet poorly crafted digital content is apt to result in apathy or distraction. Traditional approaches can feel stale, too, unless presented dynamically. Each must balance the other carefully to be effective. Strategies for Effective Blended Learning Educators need to use thoughtful strategies that blend technology and traditional approaches seamlessly to succeed with a successful blend. These are some of the most important strategies: Set Clear Objectives: Set learning objectives that determine when to employ technology or conventional teaching techniques. For instance, utilize online tools for content presentation and practice, like setting online quizzes, while keeping face-to-face classes for discussion or problem-solving exercises that can take advantage of human interaction. Make Use of Technology Wisely: Select tools that supplement, not supplant, face-to-face instruction. Edmodo or Microsoft Teams can be used to allow collaboration, while virtual simulations can allow further exploration of difficult concepts. But make sure that technology has a definite end in mind, such as supporting a lesson learned in the classroom. Prioritize Interaction: Employ old-school approaches to establish relationships and develop cooperation. Group work, Socratic seminars, or peer critiques promote social learning that technology can’t exactly duplicate. Supplement these with online discussion forums to take discussions beyond the classroom. Monitor and Adapt: Leverage data from digital tools to monitor student progress and adapt instruction in response. For instance, analytics from online tests can highlight areas in which students need help, enabling teachers to teach these in classroom sessions. Student feedback regularly received can also inform adjustments to the blended model. Maintain Balance: Do not do too much of each strategy. An example, restrict the screen time so that it does not lead to burnout and ensure that the face-to-the-face activities are the necessary one. This balance can be accomplished fairly well with the help of a flipped classroom structure in which the material will be viewed online and subsequently followed by a series of interactive activities in the classroom. The Future of Blended Learning As technology evolves, so will the capability for blended learning. Emerging technologies like artificial intelligence, augmented reality, and adaptive algorithms will continue to tailor learning. But the human element—teachers’ expertise, peer-to-peer, and emotional support—will never be automated. The future is about mastering this balance, so that technology enhances, not replaces, the human connections that make learning. Institutions must also confront systemic challenges such as funding for technology and teacher training in order to maintain blended learning. Policymakers, educators, and communities all must unite and create equitable, inclusive systems that harness the best from both worlds. Read More: The Role of Social-Emotional Learning in Shaping Tomorrow’s Leaders

The Role of Social-Emotional Learning in Shaping Tomorrow’s Leaders
In an age characterized by increased technological progress and global interdependence, the characteristics of effective leadership are also changing. While technical competence and intellectual ability remain paramount, the capacity to manage intricate human interactions, create collaboration, and exhibit resilience is equally important. Social-emotional learning (SEL), an approach that focuses on the building of emotional intelligence, self-understanding, and inter-personal skills, is becoming a keystone in developing people to be leaders in the 21st century. Through the development of these skills, SEL provides future leaders with the skills to motivate, adapt, and survive in complex and dynamic settings. Understanding Social-Emotional Learning Social-emotional learning is an instructional approach that integrates five fundamental skills namely self-awareness, self-management, social awareness, relationship skills and responsible decision-making. According to the Collaborative for Academic, Social, and Emotional Learning (CASEL), these competencies are a system-wide approach to skill development through which individuals can come to better understand and manage their emotions, establish positive relationships, and make good decisions. In contrast to other academic fields, SEL focuses on so-called soft skills that create the backbone of personal and professional success and, therefore, an essential component of leadership training. The Leadership Imperative The needs of the modern leadership do not stop at the technical knowledge. The contemporary leaders should be able to deal with complex social processes, to create trust, and to move people to act collectively in ambiguous situations. The SEL directly handles these needs as it encourages emotional intelligence that is continually demonstrated through research to be linked to successful leadership. A 2019 study conducted by the Center of Creative Leadership determined leaders with high-emotional intelligence have a higher probability of building harmonious groups, encouraging innovation, and achieving organizational results. SEL in Academic Environments The inclusion into education is also an important measure in shaping up future leaders. Nowadays, SEL is also becoming a part of academic studies, as educational institutions are teaching it to students in order to help them be ready both to their professional and personal achievements. Mindfulness training, peer mentoring and problem-solving group work are examples of SEL practices that allow students to develop interpersonal and emotional resilience at an early age. For instance, a 2021 meta-analysis in Child Development showed that students involved in SEL programs demonstrated enhanced academic achievement, better mental health, and improved social skills over their peers. By cultivating SEL in the classroom, teachers provide the foundation for students to learn to work together, communicate, and problem-solve—skills that directly apply to leadership positions. For example, a student who can manage stress through SEL practices will be more able to deal with the stress of making decisions in an executive boardroom. A young adult who is schooled in empathy will be more likely to lead with empathy, inspiring loyalty and commitment among their respective teams. SEL in the Workplace The positive effects of SEL are not only limited to the classroom but also to the workplaces, and emotional intelligence in leadership development is getting more and more attention in organizations. Other companies such as Google and Microsoft have implemented SEL concepts in their training programs as they have realized that leaders that are best at self-awareness and relationship building produce improved results. For example, Google’s Project Oxygen, a study of effective management, identified emotional intelligence as a key trait of top-performing leaders, emphasizing skills like active listening and empathy. Workplace SEL programs, including team-building and leadership coaching, enable professionals to hone their capacity to work under high-stress conditions. These programs also instill a culture of psychological safety, which encourages employees to experiment and share ideas. Leaders who are trained in SEL can better create such an environment, which leads to innovation and resilience in the organization. Challenges and Opportunities Albeit its advantages, SEL implementation is problematic. Lack of resources, inadequate teacher training, and differences in attitudes toward emotion expression present obstacles to its adoption. SEL is wrongly perceived in certain areas as secondary to academic success and neglects its potential to enrich cognitive and professional performance. These impediments can be addressed by investing in teacher training, culturally sensitive curricula, and public awareness programs to promote the worth of SEL. The possibilities, though, are vast. With automation and AI transforming sectors, human skills such as empathy and flexibility are emerging as differentiators in the labor force. Those who are able to generate trust, work through ambiguity, and collaborate will be in great demand. By making SEL a priority, communities can build a next generation of leaders who are able to address the world’s greatest challenges, from social inequality to climate change, with heart and clarity. The Path Forward To maximize SEL’s potential, stakeholders should work together. Policymakers should embed SEL in national standards for education, ensuring equal access to programs. Schools and workplaces should invest in evidence-based SEL interventions, adapting them to meet multiple populations. Parents and communities can support SEL by modeling emotional intelligence and creating supportive environments. The contribution of SEL to developing tomorrow’s leaders cannot be overemphasized. By providing people with the social and emotional skills to lead with empathy, resilience, and integrity, SEL sets the stage for a more inclusive and innovative world. As the world becomes increasingly complex, the leaders who will succeed are those capable of connecting, inspiring, and evolving—abilities social-emotional learning specifically nurtures. Read More: Balancing Technology and Traditional Teaching Methods for a Blended Learning

Richard Charles Larson: A Lifelong Commitment to Optimizing Systems and Empowering Education
The world around us is changing faster than ever, yet the old problems — long waits, unequal access to opportunity, tangled systems that seem impossible to untangle — remain stubbornly in place. What’s rare now, more than just knowing the math or mastering the technology, is the ability to see the people caught up in those problems and bring both sharp analysis and genuine care to solving them. This is where Operations Research steps in: not just a set of tools, but a bridge between cold numbers and warm human needs. Among those who have walked this bridge for over sixty years stands Richard Charles Larson. He isn’t just a name in a textbook or a mind behind complex models. He’s the scholar who chose to wrestle with the chaos of city life — emergency response times, the agony of waiting in lines — with a passion that never lost sight of the individuals behind every data point. At MIT, where he taught and innovated, Richard Charles Larson earned the nickname “Doctor Queue,” not as a gimmick, but as a testament to how deeply he understood the invisible stresses woven into everyday waiting. But the man behind the models is also quietly human in ways you might never expect. Take his walks in the Massachusetts woods, where the only sound besides the rustling leaves is the soft padding of Maisie, his golden retriever. There, away from graphs and algorithms, Larson finds the space where intellect meets reflection — a reminder that every equation has a heartbeat. His life’s work is proof that the greatest advances come not from cold logic alone, but from pairing it with kindness and a sincere wish to make the world better. Let’s dive into the story of a visionary whose passion for teaching and problem-solving revolutionized waiting times, education access, and operational systems globally! From Applied Mathematics to Lifelong Teaching Larson’s journey started in the classrooms of MIT, where he was a graduate student studying applied mathematics. At first, his focus was on complex theories and abstract problems, but it didn’t take long for him to realize that what truly mattered was helping students understand difficult concepts. He found great satisfaction in those moments when a student’s confusion gave way to clear understanding—seeing that shift became a driving force in his work. Over time, this experience shaped his belief that education is much more than just acquiring knowledge; it’s a tool that can open doors and create opportunities, especially for those facing economic hardships. Unlike material things, education can’t be taken away, and it has the power to change lives. This idea stayed with Larson throughout his career and inspired him to dedicate himself to making learning accessible and meaningful for everyone. The Birth of Operations Research as Public Service In the 1960s, Larson emerged from the halls of academia to make a tangible difference in the real world. Partnering with the RAND Corporation, he undertook a pioneering project to model emergency services in New York City. His work applied the principles of queueing theory and operations research to the deployment of police, ambulance, and fire services — optimizing their response times and saving countless lives. This was not merely an academic exercise; his models transformed how cities approached emergency logistics, ensuring that help arrived faster when seconds could mean the difference between life and death. His innovations were so influential that he was inducted into the National Academy of Engineering, recognized for his leadership in applying mathematical methods to critical public services. Doctor Queue Unlocking the Psychology of Waiting Among the general public, Richard Charles Larson became widely known as “Doctor Queue,” a nickname that reflects his expertise in queueing theory — the study of waiting lines, bottlenecks, and delays. But his insights extended beyond the numbers. He discovered that the experience of waiting is shaped far more by psychology than by the actual time spent. “People would rather wait ten minutes if they can see what’s happening than five minutes in the dark,” he explained in countless interviews. Transparency, fairness, and distractions can all ease the frustration of waiting, turning an often exasperating experience into one that feels tolerable, even just. This blend of hard data and empathy captured the public imagination and brought a human face to a technical field. Shaping the Future of Education Through Technology In the 1990s, Richard Charles Larson shifted his focus toward education itself, recognizing the transformative potential of technology to bridge gaps in access and quality. As Director of MIT’s Center for Advanced Educational Services (CAES), he spearheaded innovative approaches that went beyond traditional lectures. One of his most notable contributions is MIT BLOSSOMS (Blended Learning Open Source Science or Math Studies), an interactive platform of video lessons designed for global accessibility. Inspired by his visit to a remote village school in China, Larson envisioned lessons that were not passive but engaging, incorporating pauses for discussion to foster active learning among teachers and students alike. Today, BLOSSOMS reaches students across dozens of countries, especially in regions where quality STEM education is scarce. His philosophy was clear: ignite curiosity, don’t just convey information. LINC: Building Global Educational Bridges Not content with developing content alone, Richard Charles Larson founded the Learning International Networks Consortium (LINC) in 2002, a global network that connects educators, policymakers, and practitioners from over 25 countries. LINC fosters collaboration and knowledge exchange to harness technology in overcoming geographic and economic educational barriers. Through LINC, MIT partnered with the Government of Punjab, Pakistan, to incorporate BLOSSOMS into public secondary schools — a move that demonstrably improved STEM learning outcomes. This initiative exemplifies his broader vision of education as a universal human right and a driver of social mobility. A Prolific Scholar and Mentor Richard Charles Larson has authored more than 175 research articles and six books, addressing topics ranging from e-learning and emergency services to energy management. His work has had a significant impact on policies and practices across various sectors, including smart grids
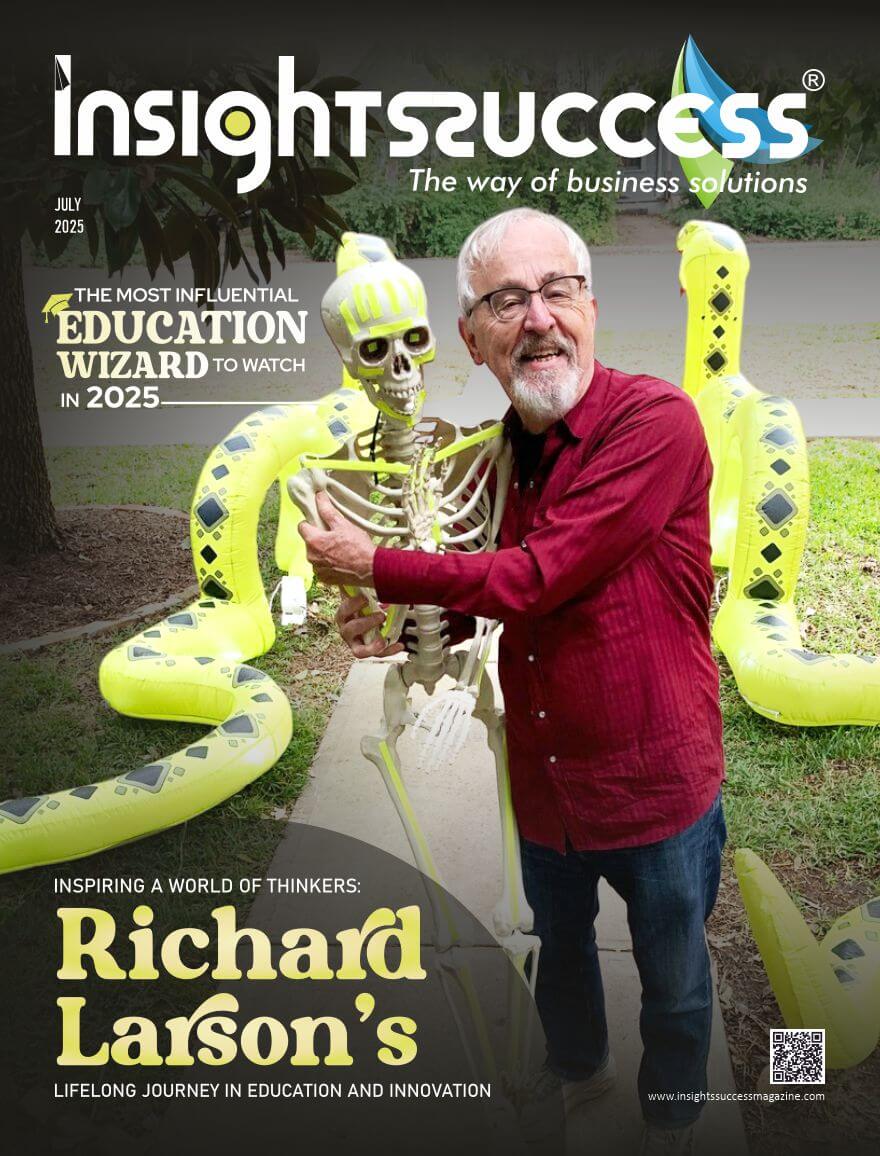
The Most Influential Education Wizard to Watch in 2025
The Most Influential Education Wizard to Watch in 2025 Known globally as “Dr. Queue” for his groundbreaking work in operations research, Professor Richard C. Larson has long been a towering figure in engineering and analytics. But in 2025, he’s being celebrated for something equally transformative: his visionary impact on global education. Honored as The Most Influential Education Wizard to Watch, Larson continues to inspire as a force redefining how we teach, learn, and lead. Quick highlights Quick reads

Inspiring a World of Thinkers: Richard Larson’s Lifelong Journey in Education and Innovation
Richard Larson’s name is synonymous with lifelong learning, innovation, and academic rigor. His journey through research, education, and public service offers a vivid illustration of how one person’s relentless pursuit of knowledge can create meaningful change in both local and global communities. Over the decades, Larson has built a legacy that spans across disciplines—from pioneering work in queueing theory to leadership in educational reform and MODEL-Based Thinking. But more than the accolades and positions, it’s his mindset—curious, compassionate, and committed—that has made the most impact. His contributions have gone beyond university corridors and academic journals. Richard Larson has always believed that education is a transformative force, capable of empowering individuals regardless of background. His commitment to making knowledge more accessible to a broader audience has defined his post-retirement years, particularly through his book MODEL THINKING For Everyday Life. Even today, long after his tenure in academia, he continues to engage, teach, and inspire through public forums and media platforms. In many ways, Richard Larson’s story is not just one of personal achievement, but also of enduring service to the idea that learning should never cease. Rooted in values of curiosity, discipline, and empathy, his work continues to influence the next generation of thinkers, educators, and innovators. His is a voice that champions not only academic excellence, but also humanity’s shared potential to learn, grow, and thrive. Academic Roots and MIT Years Richard Larson credits his journey in academia to his early admission to MIT at just 18 years old. Coming from Needham High School, he entered MIT with the support of his family, although finances were tight. While his father initially hoped he would commute, Larson joined the Phi Beta Epsilon fraternity, a decision that proved transformational. The fraternity was located on MIT’s Memorial Drive, offering both convenience and a tightly knit support system of peers. Immersed in a vibrant academic culture, Richard Larson soon discovered his passion for systems and structures, which led him to pursue graduate studies and eventually a PhD in Operations Research. A pivotal moment in his career came when his faculty advisor, Professor Alvin W. Drake, invited him to stay on as an Assistant Professor—an offer that surprised him. He grappled with imposter syndrome, wondering if he truly belonged in a faculty role so soon after graduating. However, his deep intellectual curiosity pushed him to accept. Larson rose through the academic ranks with integrity and excellence. He remained at MIT for the entirety of his professional career, drawn by the institution’s ecosystem of innovation and the joy he found in research, collaboration, and teaching. Teaching as a Calling Throughout his academic career, Richard Larson found his greatest fulfillment in teaching and mentoring. While lecturing brought its own rewards, it was the one-on-one engagement with students that he valued the most. Larson deeply enjoyed supervising research projects, guiding graduate students, and witnessing the evolution of curious learners into groundbreaking thinkers. He believed that true education involved more than just content delivery—it required fostering a mindset of critical inquiry, encouraging creativity, and instilling intellectual rigor. Many of his former students have gone on to become thought leaders in their fields, and Larson takes immense pride in knowing he played a role in their development. Richard Larson often emphasized that the role of an educator is to inspire and ignite passion for learning, not just to disseminate facts. He considered mentoring to be a reciprocal relationship where he too learned from the perspectives and questions posed by his students. Championing Future Innovators Although retired from teaching, Richard Larson continues to be an advocate for public intellectual engagement. His recent work has focused on simplifying complex ideas for broader audiences. His book, MODEL THINKING For Everyday Life, encapsulates this mission. In it, he explains how conceptual models—frameworks for understanding reality—can help individuals make better decisions, solve problems more effectively, and engage more critically with the world. He views MODEL-Based Thinking as an essential life skill. By making these models accessible, he hopes to cultivate analytical reasoning and structured problem-solving in people from all walks of life. This effort reflects his larger belief: education should empower, not intimidate. Learning as a Lifelong Habit Richard Larson firmly holds that learning is a lifelong endeavor. Echoing Einstein, he often says, “A day without learning is a day wasted.” For him, learning isn’t limited to the classroom or academic texts. It can arise from the simplest daily experiences or the most complex research challenges. Some of his most significant breakthroughs, such as the Hypercube Queueing Model, originated in unexpected places—even in dreams. Twice, he awoke with solutions to complex problems, including one instance where he documented a groundbreaking idea at 3:00 AM. These events confirmed his belief that the mind never truly stops learning, even in sleep. Richard Larson urges others to remain open and curious. He believes that maintaining a mindset of inquiry keeps individuals intellectually agile and emotionally grounded. Whether it’s observing animal behavior or engaging in scholarly pursuits, he sees every moment as an opportunity for discovery. Broadening Educational Access Beyond his work at MIT, Richard Larson has made substantial contributions to education access. He has supported initiatives aimed at expanding educational resources to underrepresented communities, such as Notre Dame Cristo Rey High School. His belief is firm: education should not be a privilege of the few but a right of the many. One of his enduring contributions to MIT is the establishment of the Richard Larson Chair in Data, Systems, and Society. This endowed faculty position supports research and teaching in areas critical to modern technological and social systems. It is his way of ensuring that MIT continues to cultivate excellence long after his tenure. His philosophy is clear—education should be a catalyst for social equity, enabling all individuals, regardless of background, to realize their potential. Facing and Overcoming Challenges Even a career as illustrious as Richard Larson’s has not been without its struggles. One humbling episode occurred early in his teaching career when he was unable to

From Classrooms to Communities
Expanding the Impact of Educational Leadership In the past, educational leadership was confined to school walls or corridors. Principals, superintendents, and curriculum coordinators were curriculum stewards, disciplinarians, and school performance stewards. But in a world characterized by quick-paced change, social complexity, and interdependent challenges, the impact of education has to be far beyond the school walls. Today’s educational leaders are not administrators alone but indeed architects of social progress. They influence not only students and staff, but communities as a whole. That is the reason why educational leadership is also being transformed—from managing instruction to governing learning ecosystems, well-being, and equity at an increased level. Education as a Community Engine Learning does not occur in a void. Every school exists in a socio-economic, cultural, and political context. Issues like poverty, mental illness, hunger, digital divide, and environmental uncertainty directly influence student performance and parental engagement. The educators of today’s time observe that schools are not independent entities, but community centers—sites of intersection among public health, technology, social services, and local government. Thus, educational leadership is now the ability to collaborate across sectors, build the trust of the community, and advocate for policy changes that improve the context for learning. By taking their work beyond school management to community leadership, teachers today are reshaping schools as agents of holistic development, turning institutions where learning is supported by helping hands and collective responsibility. Leading with Equity at the Core Most indicative of strong educational leadership today may be a deep commitment to equity and inclusivity. Leaders must not simply close gaps in achievement but also address the structural barriers that generate them—whether along racial, income, geographic, or ability lines. That requires confronting hard truths, dismantling systemic inequities, and making sure all students have access to quality education regardless of background. That requires courage, cultural competency, and the ability to create policies that are data-informed and people-focused. From implementing restorative justice and inclusive curriculum to pushing for diverse hiring and culturally responsive teaching, educators are rising to become social justice leaders, reforming schools into safe and empowering communities for all. The Shift to Community-Based Models of Leadership The new educational leadership model is fundamentally collaborative. Top-down dictum is no more; instead, distributed leadership models take center stage where teachers, parents, students, civic leaders, and nonprofit organizations are all involved in collaborative decision-making. Leaders are transforming themselves into partnership facilitators, accessing local industry for internships, working with health clinics for school-based services, and working with municipal departments on public safety, transportation, and housing initiatives. These collaborative efforts recognize that student success is inextricably tied to the well-being of the community, economic growth, and civic engagement. By building coalitions and working together to create solutions, educational leaders become bridge-makers, linking academic aspirations with community aspirations. Technology as a Force for Community Engagement Technology is today a force to be recognized in broadening the scope and impact of educational leadership. From virtual town halls and parent portals to AI-driven learning environments and real-time data analytics, leaders today are more attuned to student and community needs than ever before. But with this visibility comes responsibility. Effective leaders use digital tools not just to monitor performance but to raise voices, generate openness, and enable real engagement with families and community constituents. They gain digital equity by bridging gaps in access and making edtech that serves all learners, not just the fortunate few. By that standard, digital leadership is not about adopting the newest platform—it’s about using technology to make connections more human and expand opportunities for learning. Leadership Growth for a Broader Mission As educational leadership expands its focus, so must the way leaders are prepared, guided, and developed. Leadership development for the future requires that programs look beyond instructional strategy to include community building, cultural competence, change management, systems thinking, and advocacy of public policy. Mentorship, cross-sector internships, and peer learning networks can be the solution to empowering leaders to manage the intersectional challenges they will face. Educational institutions and governing bodies must also redefine leadership not just as a vocational aspiration, but as a civic responsibility—one which can shape the very fabric of communities at large. Conclusion: A New Era of Influence The most effective education leaders today lead not only by doing, but by mobilizing. They see every student as part of a broader community and every school as a force for social transformation. They think beyond the classroom, beyond the semester, and even beyond the school district. By committing to a larger, braver vision of leadership—one that is based on equity, community, and systems change—these leaders are recasting the very mission of education. They are reminding us that schools are not merely places for learning, but springboards for lives, bridges for communities, and changemakers for futures. In the changing landscape of education, leadership that connects classrooms to communities is not only worth its weight in gold—it is priceless.

EdTech Needs EdLeaders
Guiding Schools into the Digital Age Education stands at a crossroads. Technology breakthroughs—formerly on the periphery of the system—are now squarely in the center of the way students learn, teachers teach, and schools operate. From artificial intelligence learning labs and computer-adaptive testing to virtual reality classrooms and adaptive curriculum, educational technology (EdTech) is transforming the classroom. But whereas EdTech can transform learning, success will hinge on something deeper: inspirational educational leadership. Without visionary, compassionate, and future-oriented leaders, even the most sophisticated technologies can collapse or be applied for evil. To achieve the promise of digital transformation, EdTech needs EdLeaders—those with pedagogy and innovation knowledge, capable of effecting change with front and foremost in mind the human experience of learning. It is not just a buying problem to get technology into the schools. It is a change in culture—a change that encompasses equating tools with learning objectives for students, restructuring the role of teacher, redefining assessment paradigms, and instructing students about digital citizenship. This shift needs to be led, not mandated. School administrators have the opportunity to shape how technology is perceived and harnessed in their own schools. They must flip the conversation from devices and apps to purpose and pedagogy: How does this tool enable teaching? How will it aid equity? What success looks like? Through the injection of a purpose-innovation attitude, EdLeaders keep digital initiatives founded on the values of innovation and not technology trends. Vision, Strategy, and Digital Literacy Effective digital leadership begins with a vision—a vision that outlines how technology will enhance student success, support teachers, and prepare students for life in the digital world. Vision alone, however, is not enough. Leaders need to build effective strategies that solve for infrastructure, staff development, digital equity, security, and ongoing assessment. This requires profound digital literacy on the part of school leaders themselves. They must know the capabilities and limitations of EdTech tools, data privacy, and the ethics of AI in educational settings. Above all, they must be able to distinguish between substance and hype. Informed leadership enables schools to make smart investments, avoid vendor-led decision-making, and focus on student-centric transformation rather than glitzy change. Empowering Teachers for the Digital Shift Teachers are the EdTech success frontline heroes, but it is unrealistic to expect them to shoulder this transition by themselves. Edtech Leaders must ensure that a culture of support is facilitated whereby teachers are enabled rather than restricted by digitalization. It is an investment in ongoing professional development that goes beyond tool tutorial training and into instructional design for technology-enabled, personalized, and inclusive learning. It is an investment in recognizing that not every teacher will be as digitally confident—and providing differentiated support accordingly. When teachers are placed front and center in digital planning by putting teacher voice and agency first, they ensure a culture of trust and risk-taking with shared innovation rather than direction. Equity as a Foundational Value One of the greatest expectations of EdTech is that it can close knowledge gaps by making access available to materials, personalized learning, and increased flexibility. Without intentional leadership, however, technology also has the ability to make existing inequalities worse—everything from connectivity and device access to language and algorithmic bias. Educational leaders must place digital equity at the top of their EdTech priority list. That involves not just offering all students access to the tools and the internet they require but also inclusive platforms, culturally sensitive content, and special accommodations for marginalized populations. Equity leadership ensures that digital transformation works for all learners, not just the digitally privileged. Building Stakeholder Trust The integration of EdTech impacts not only students and teachers but also parents, school boards, community partners, and policymakers. Leaders need to communicate actively, engage themselves, and establish trust among all involved stakeholders in order to secure long-term success. That includes defining the “why” of digital efforts, addressing privacy head-on, and sharing quantifiable results in straightforward language. If parents get to see how a new platform is enhancing their child’s education—or how AI-powered tools are being applied responsibly—they become allies, not adversaries, to the effort. Open leadership fosters an adopter community for technology and injects accountability into each step of the way. Conclusion: EdTech Needs More Than Tech Learning in the future will be technology-driven—but human-driven. And spearheading this transformation are EdLeaders—leaders who can steer schools through complexity, power innovation with intention, and put students at the center of every decision. In times when digital literacy is on par with literacy and numeracy, EdLeaders are the ones to strike a balance between tradition and transformation. They’re the designers of learning environments that are networked, inclusive, and forward-looking. For in this era of computer technology, it’s not a matter of technology adoption. It’s about leading it—with vision, integrity, and an unshakeable faith in educational excellence. Read More: From Classrooms to Communities

Digital Beachhead Quarterly Magazine, 2025
Digital Beachhead Quarterly Magazine, 2025 Aiming to inform, inspire, and ignite meaningful dialogue, the publication engages digital leaders, policymakers, defense professionals, and technology innovators. It serves as a rallying point for those navigating the complex and rapidly shifting terrain of digital conflict, innovation, and strategic transformation. Quick highlights Quick reads

Cyber Resilience and Why it Matters
CEO Corner – Mike Crandall In a world where digital infrastructure underpins nearly every aspect of our lives, from critical national services to our daily banking and communication, it’s no longer enough to focus solely on cybersecurity. As threats grow more sophisticated and persistent, the conversation has shifted from preventing breaches to surviving them. Enter cyber resilience, a concept that is fast becoming the cornerstone of modern digital strategy. What Is Cyber Resilience? Cyber resilience refers to an organization’s ability to continuously deliver the intended outcome despite adverse cyber events. It encompasses not only the capability to defend against attacks but also to respond, recover, and adapt in their aftermath. Think of it this way: cybersecurity is the armored door that tries to keep intruders out. Cyber resilience, on the other hand, is the entire fortified house—designed not only to deter break-ins but also to limit damage, ensure recovery, and learn from each attempted intrusion. Why Cyber Resilience Matters More Than Ever Attacks Are Inevitable Despite the best defenses, cyber incidents are increasingly unavoidable. Phishing attacks, ransomware, data breaches, and zero-day exploits bypass even well-maintained systems. Resilience ensures that when—not if—a breach occurs, the fallout is manageable. Downtime Is Expensive A single hour of IT downtime can cost enterprises thousands, if not millions, of dollars. Beyond financial loss, service interruptions damage reputation, customer trust, and even regulatory standing. Resilience strategies, including failover systems and data backups, can significantly reduce recovery times. Compliance and Regulation Governments and industries are introducing stricter cybersecurity regulations. Frameworks like the NIST Cybersecurity Framework, GDPR, and CISA guidelines emphasize not just prevention but resilience. Being cyber resilient is now a matter of legal compliance in many sectors. Business Continuity and Reputation How an organization handles a cyber incident often matters more than the incident itself. A fast, transparent, and effective response can preserve trust and market position. Failure to act quickly—or at all—can lead to long-term damage. The Pillars of Cyber Resilience Building cyber resilience is not a one-time project; it’s a dynamic process that involves people, technology, and culture. Here are the key components: Risk Assessment: Understand what assets are most critical and which threats are most likely to affect them. Incident Response Planning: Develop and regularly test response plans so that teams know exactly how to act during a crisis. Continuous Monitoring: Employ tools and practices that provide real-time visibility into systems and detect anomalies quickly. Backup and Recovery: Regularly backup data and ensure systems can be restored efficiently. Training and Awareness: Educate employees on best practices and make security a shared responsibility across all departments. Supply Chain Security: Ensure vendors and partners meet security standards, as third-party risks are a growing concern. Building a Culture of Resilience True resilience starts at the top. Leadership must prioritize cyber resilience as part of the overall business strategy. Investment in the right tools and talent, ongoing education, and regular testing of systems and protocols are essential. Moreover, fostering a culture where employees feel empowered and responsible for cyber hygiene can transform resilience from a technical challenge into an organizational strength. Conclusion Cyber resilience isn’t just a buzzword—it’s a business imperative. In a landscape where threats evolve daily, being resilient means being prepared, adaptable, and always one step ahead. For businesses, governments, and individuals alike, the goal is no longer to build walls tall enough to prevent every breach, but to become strong and flexible enough to withstand, recover, and grow from whatever comes next. As the saying goes: “Resilience is not about avoiding the storm, it’s about learning to dance in the rain.” Want to build a more cyber-resilient organization? Contact us at Digital Beachhead, www.digitalbeachhead.com to start with a risk audit, train your employees, and explore frameworks like NIST or ISO 27001 to help guide your journey. Read More: Cloud Apps Management: Is Your Business in Control?




